Data breach
When your data is stolen – definition, motives, and the complex investigation
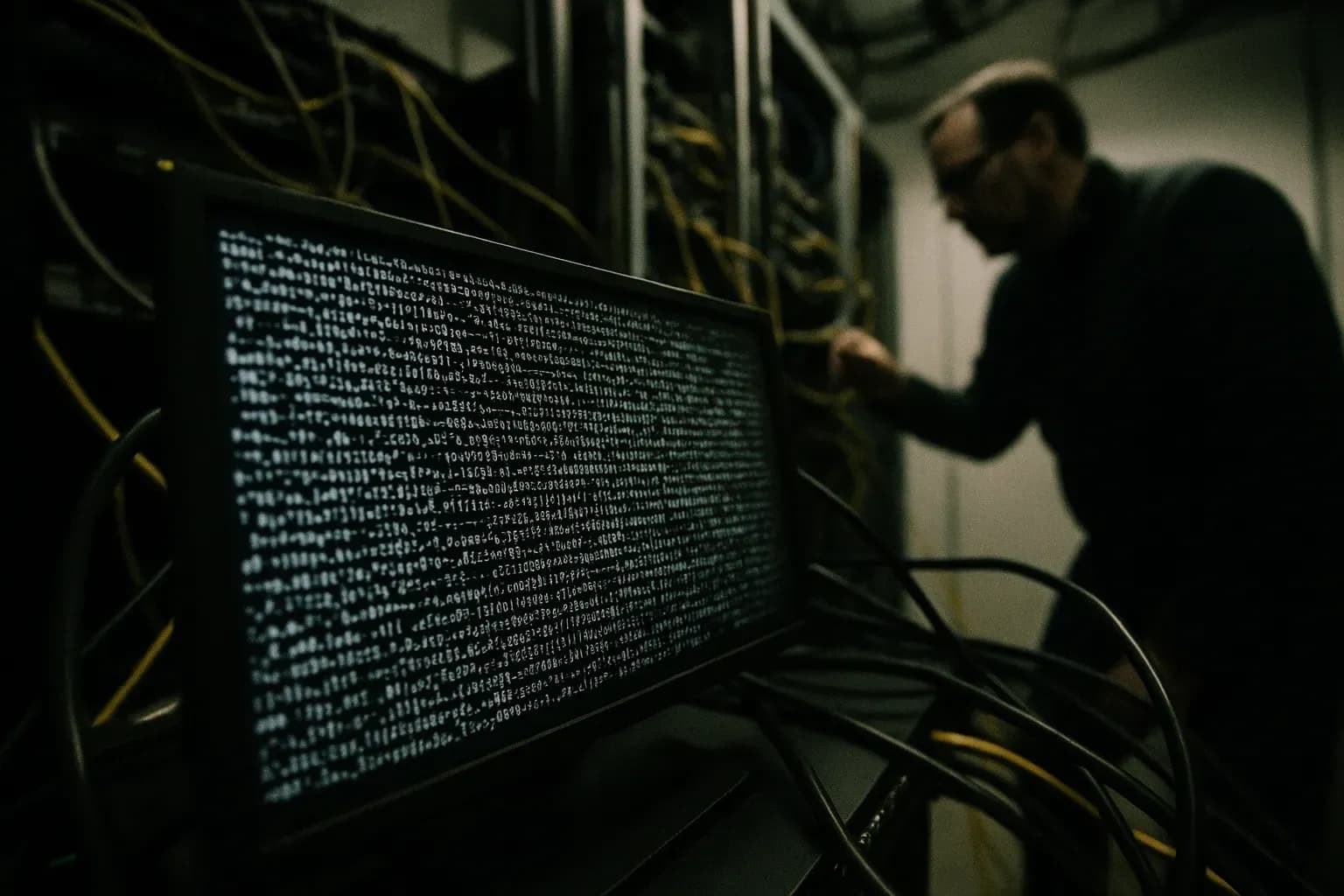
Data breaches revealed: Understand what happens when sensitive information falls into the wrong hands, the motives behind them, and why they are central to true crime.
When your data is stolen – definition, motives, and the complex investigation
What is a data breach and why is it key to cybercrime?
In true crime, a data breach is defined as an incident where sensitive, protected, or confidential data is compromised through illegal access, copying, transmission, theft, or use by an unauthorized party. Far from being merely a technical mishap, a data breach often forms the core of modern cybercrime, with potentially far-reaching and devastating consequences for individuals, businesses, and government institutions. This makes the investigation of data breaches a central element in many criminal cases.
From financial gain to espionage: Data breach motives
The motives behind a data breach are diverse and can include financial gain through the sale of stolen personal information, credit card details, or login credentials on the dark web, which often leads to extensive identity theft with severe consequences for victims' finances and reputations. Other perpetrators use the compromised data for extortion, commit industrial espionage to gain competitive advantages, or engage in state-sponsored hacking for political or intelligence purposes. The data compromised in a breach can include a wide range of information: from deeply personal data such as personal identification numbers, financial information, and health records, to critical business secrets, intellectual property, and even national security information. This spectrum of potentially stolen data underscores the immense severity and far-reaching dangers associated with a data breach.
Victims' nightmares and investigators' fight: Cybercriminals
For victims of a data breach, the consequences can be long-lasting and deeply personal, including financial losses, significant emotional distress, and an often grueling battle to restore their identity and digital security. Organizations affected by a data breach face potentially enormous financial costs, loss of customer trust, severe reputational damage, and extensive legal repercussions. The investigation of data breaches itself is an extremely complex digital forensic process, where specialized cybercrime units must navigate a global network of anonymization techniques, encrypted systems, and jurisdictional barriers to track down and prosecute those responsible. A thorough understanding of data breaches is therefore essential in modern true crime, as this form of cybercrime represents an ever-growing and often invisible threat, whose technical complexity and severe consequences continue to challenge both investigators and societal efforts to improve information security and protection.
From stolen credit card details to extensive corporate espionage. What do data breaches look like in practice? Read our harrowing case studies on the subject below.